The AI Chips Traceability Chokepoint
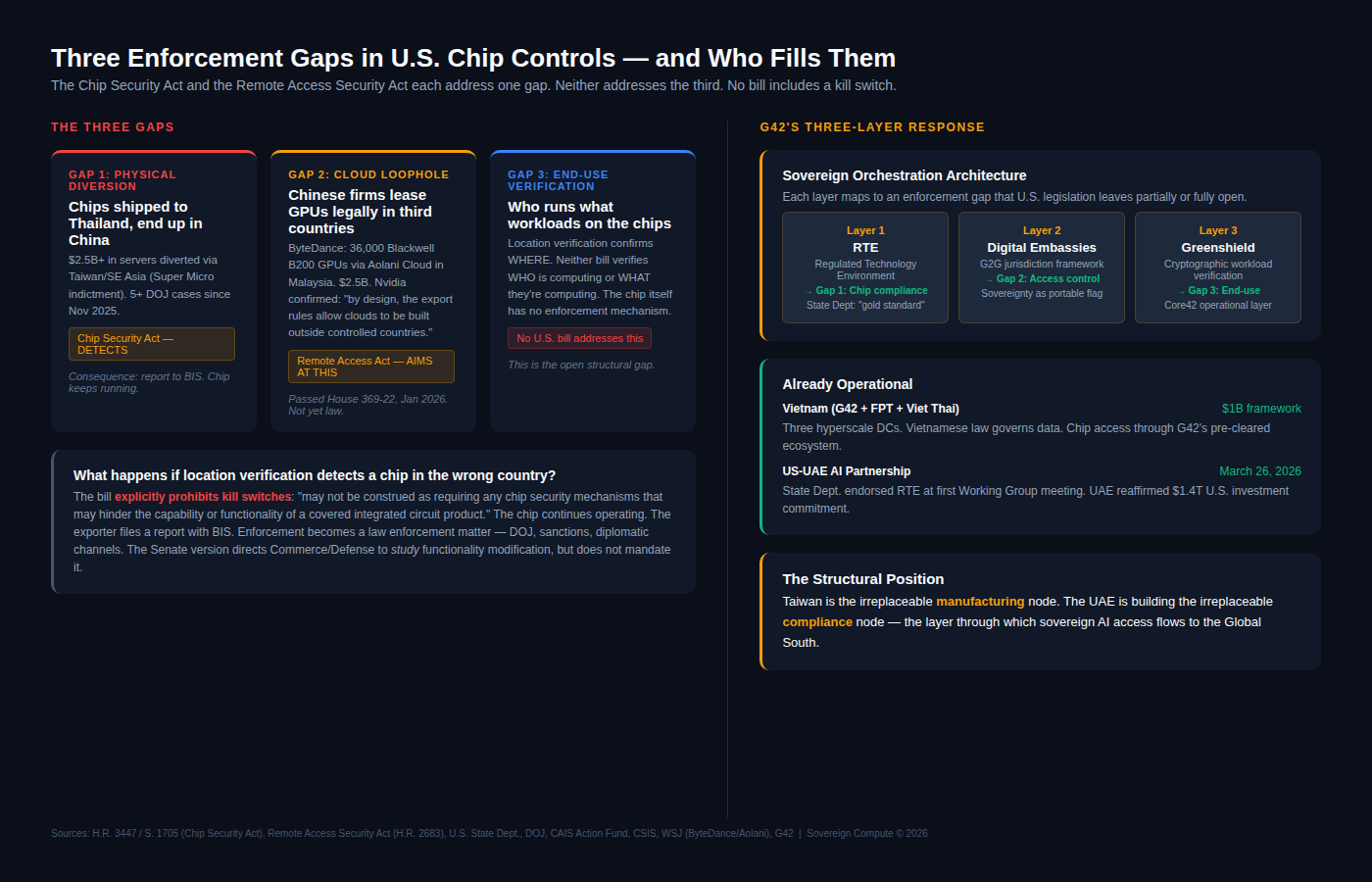
The CSA detects diverted chips but cannot disable them. The RAA targets the cloud loophole but hasn’t passed the Senate. Neither verifies who’s running workloads. The UAE is exporting a solution.
Washington is addressing chip enforcement in two halves: location verification and remote access controls. The third gap — end-use verification at the workload level — remains open in U.S. legislation. G42 built an operational layer for it.
On March 26, the House Foreign Affairs Committee advanced the Chip Security Act, a bill requiring location verification mechanisms embedded directly into every advanced AI chip before export.
The legislation advanced one week after prosecutors unsealed the indictment of Super Micro’s co-founder for conspiring to divert $2.5 billion worth of Nvidia servers to China through Taiwan and Southeast Asian intermediaries. Since November 2025, the Department of Justice has brought at least five separate smuggling cases involving fake audit servers, shell companies in Florida, and routing through Malaysia and Thailand. The Chip Security Act addresses this specific problem: physical diversion of chips from authorized destinations. Ping-based location verification, using network latency triangulation across a dozen geographically dispersed servers, can confirm a chip’s country-level position with roughly 60-mile accuracy. Working prototypes already exist on Nvidia H100 chips. Nvidia has acknowledged its GPUs already transmit the telemetry data needed for this, and implementation could come through a firmware update.
The enforcement question, though, is what happens when verification detects a chip in the wrong country. The bill’s text explicitly prohibits kill switches: it “may not be construed as requiring any chip security mechanisms that may hinder the capability or functionality of a covered integrated circuit product, such as a kill switch or geofencing mechanism.”
The chip keeps running. The exporter is required to report the discrepancy to the Bureau of Industry and Security. After that, enforcement becomes a law enforcement matter — DOJ investigations, sanctions, diplomatic channels. The Senate version directs Commerce and Defense to study whether future mechanisms could “modify the functionality” of illicitly acquired chips, but that assessment is at least a year away from any mandate. For now, detection and reporting is the entire enforcement architecture. Spoofing individual chips through latency manipulation is possible; spoofing thousands of GPUs simultaneously in a data center cluster is substantially harder, though the Center for Cybersecurity Policy has warned that any embedded verification mechanism introduces new attack surfaces that hostile actors could exploit.
Location verification addresses physical diversion. It does not address a second, arguably larger gap: Chinese companies legally accessing advanced chips in third countries. In March, the Wall Street Journal reported that ByteDance is deploying 36,000 Nvidia Blackwell B200 GPUs through Aolani Cloud in Malaysia — a $2.5 billion cluster that will be among the largest commercial AI deployments in Southeast Asia. The chips stay in Malaysia. They are formally owned and operated by a Malaysian entity. Nvidia confirmed the arrangement complies with export controls, noting that “by design, the export rules allow clouds to be built and operated outside controlled countries.” Location verification would confirm these chips are exactly where they are supposed to be. The problem is that ByteDance’s engineers access the compute remotely from China. The House passed the Remote Access Security Act 369–22 in January 2026 to close this “cloud loophole” by extending export controls to cover remote access to controlled chips. It has not yet cleared the Senate, and enforcement — monitoring who logs into every GPU cluster globally — is substantially more complex than verifying where hardware sits.
A third gap remains fully unaddressed by either bill. The Chip Security Act verifies where chips are. The Remote Access Security Act, if passed, would regulate who accesses them remotely. Neither verifies what workloads are running on the chips or whether the entity operating them is the authorized end user in practice, not just on paper. A Malaysian cloud operator that leases capacity to a Chinese AI lab is legal under current rules, and neither bill’s enforcement mechanism reaches the workload layer. This is the structural opening that G42’s compliance architecture occupies. The Regulated Technology Environment handles chip-level compliance — the State Department described it as a “gold-standard framework for managing sensitive technologies” at the first U.S.-UAE AI Acceleration Partnership Working Group meeting on March 26. The April 6 State Department readout went further, describing the RTE as operating under “jointly agreed security and governance requirements”. Digital Embassies, launched at Davos in January, establish government-to-government legal constructs that define who has jurisdictional authority over AI workloads, regardless of where infrastructure is physically located. And crucially, Microsoft serves as the primary infrastructure partner for this framework, reinforcing the UAE’s position as a collaborative node for U.S. technology rather than a sovereign replacement for it.
Greenshield, the operational layer run by Core42, applies cryptographic controls that verify where workloads are processed and ensure they remain within authorized sovereign environments. Together, the three layers create an end-to-end compliance architecture that covers physical location, access control, and workload verification — the full stack that U.S. legislation, taken together, still leaves partially open.
The Vietnam deal shows the model already scaling. In February, G42 signed a $1 billion framework agreement with FPT Corporation and Viet Thai Group to deploy three hyperscale data centers with full sovereign cloud capacity. Vietnam gets AI infrastructure without negotiating chip allocations or export licenses with Washington directly — it buys into a G42-managed ecosystem that has already cleared those compliance hurdles across all three layers.
The Atlantic Council’s William Wechsler argued this month that the Gulf’s interdependence with the West extends far beyond energy, noting the region “will have a disproportionate role in the future of the global infrastructure for artificial intelligence, just as Taiwan today plays an outsize role in semiconductors.” Taiwan’s leverage is its position as the irreplaceable manufacturing node. The UAE is building the analogous position for compliance: the node through which verified sovereign AI access flows to the Global South.
The critical question for policymakers and infrastructure investors: if chip traceability becomes the global standard for hardware access — and bipartisan momentum suggests some version will — then verified compliance infrastructure replaces raw chip supply as the binding constraint on sovereign AI. The Semiconductor Industry Association and the Information Technology Industry Council are right that mandated tracking could push some buyers toward Chinese alternatives. That risk strengthens the case for a trusted intermediary that keeps nations inside the U.S. technology stack while providing sovereign control at the workload level. Five federal smuggling cases, a $2.5 billion legal cloud workaround in Malaysia, and an open gap at the end-use layer all point in the same direction. Whoever controls the compliance architecture that determines where, by whom, and for what purpose GPUs operate holds the next structural advantage in sovereign AI.
Sources
• H.R. 3447 / S. 1705 — Chip Security Act, 119th Congress (congress.gov)
• H.R. 2683 — Remote Access Security Act, passed House 369–22, January 12, 2026 (eeNews Europe)
• House Foreign Affairs Committee press release, March 26, 2026
• U.S. State Department — First U.S.-UAE AI Acceleration Partnership Working Group, April 6, 2026
• CAIS Action Fund — “The Chip Security Act: Separating Fact From Fiction”
• CSIS — “The Architecture of AI Leadership,” February 2026
• Center for Cybersecurity Policy & Law — analysis of CSA cybersecurity risks, July 2025
• Foundation for American Innovation — “The Chip Security Act: A Bipartisan Solution,” July 2025
• Wall Street Journal — ByteDance / Aolani Cloud / Blackwell deployment, March 13, 2026
• Tom’s Hardware — Nvidia confirmation: “export rules allow clouds outside controlled countries,” March 2026
• BISI — “AI Chip Smuggling: The Limits of US Export Controls,” April 6, 2026
• SIA Statement on Chip Security Act, March 2, 2026
• ITI — “The Unintended Consequence of the Chip Security Act,” February 27, 2026
• G42 — Digital Embassies and Greenshield launch, January 20, 2026 (Davos)
• G42 / FPT / Viet Thai Group Framework Agreement, February 9, 2026
• Atlantic Council — William F. Wechsler, “Why the Gulf Should Keep Looking West,” April 2026
A note on independence: All opinions shared in this newsletter are my own and do not reflect the views of dmg events, ADIPEC, or any affiliated organizations. This is personal analysis, not institutional positioning.